Packet Filtering Firewall - AR100, AR120, AR150, AR160, AR200, AR1200, AR2200, AR3200, and AR3600 V200R010 CLI-based Configuration Guide - Security - Huawei
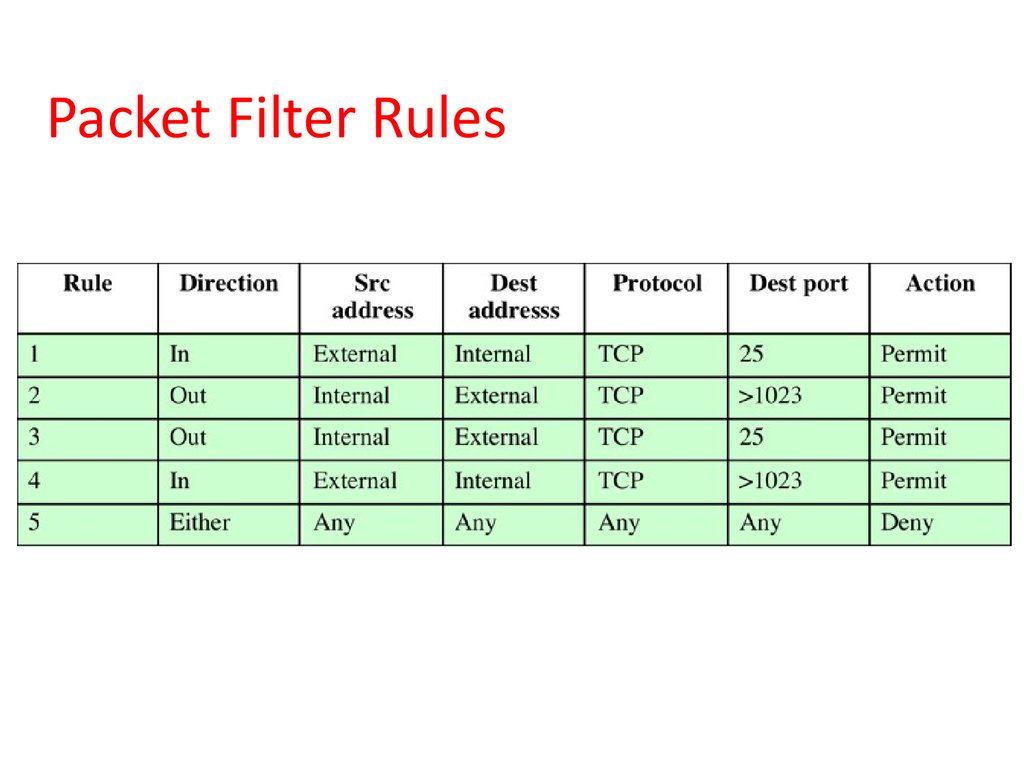
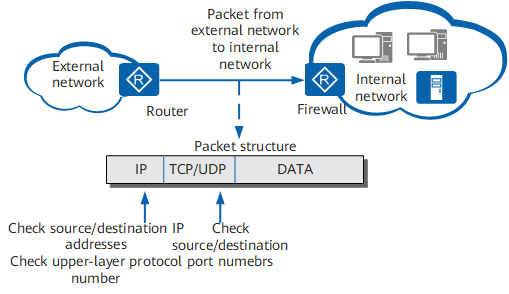
Computer Security: Principles and Practice. Firewalls and Intrusion Prevention Systems. Chapter 9 - online presentation
Firewall Categories :: Chapter 2. Introduction to Firewalls :: Part I: Security Overview and Firewalls :: Router firewall security :: Networking :: eTutorials.org
Firewall Categories :: Chapter 2. Introduction to Firewalls :: Part I: Security Overview and Firewalls :: Router firewall security :: Networking :: eTutorials.org



![Chapter 6] Packet Filtering Chapter 6] Packet Filtering](http://web.deu.edu.tr/doc/oreily/networking/firewall/figs/fire0601.gif)











![Packet-filtering firewall/stateless firewall - CCNA Security 210-260 Certification Guide [Book] Packet-filtering firewall/stateless firewall - CCNA Security 210-260 Certification Guide [Book]](https://www.oreilly.com/library/view/ccna-security-210-260/9781787128873/assets/7c1dd246-f186-41d6-83df-899340505136.png)